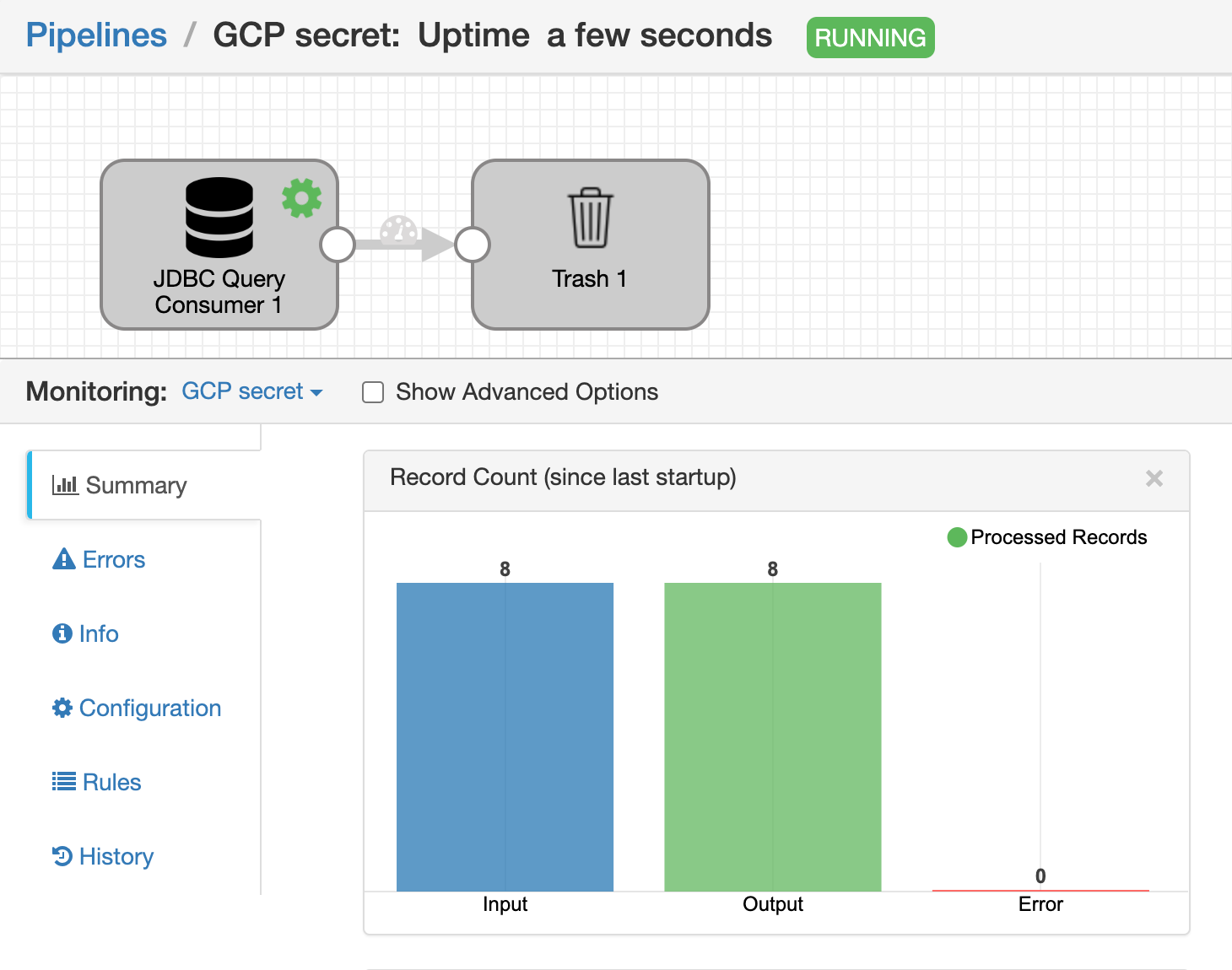
In this article, we will walk you through the necessary steps to configure and set up Google Secrets for use with Data Collector.
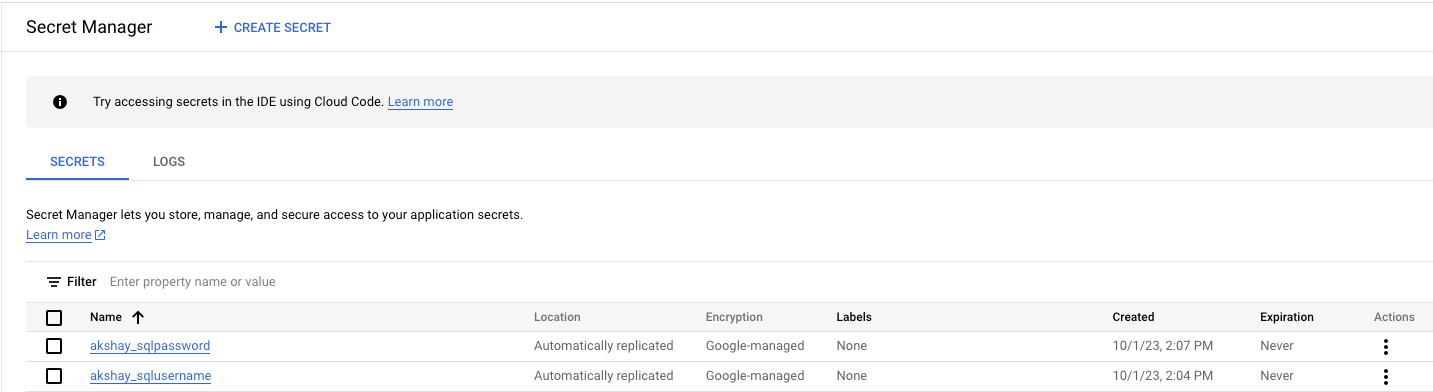
Firstly, We have to create the secret on the GCP which we will be using in the pipeline. In this article, I am going to store the mysql username and password in secrets.
These are the secret created in GCP:-
The pre-requisite is to install the package Google Secret Manager Credential Store on the Data collector and then update the following properties in credential-stores.properties file.
- credentialStores=gcp
- credentialStore.gcp.config.project.id= <gcp-projectID>
- credentialStore.gcp.config.credentialsMode=jsonPath
- credentialStore.gcp.config.credentialsJsonPath=/Users/apple/.config/gcloud/application_default_credentials.json
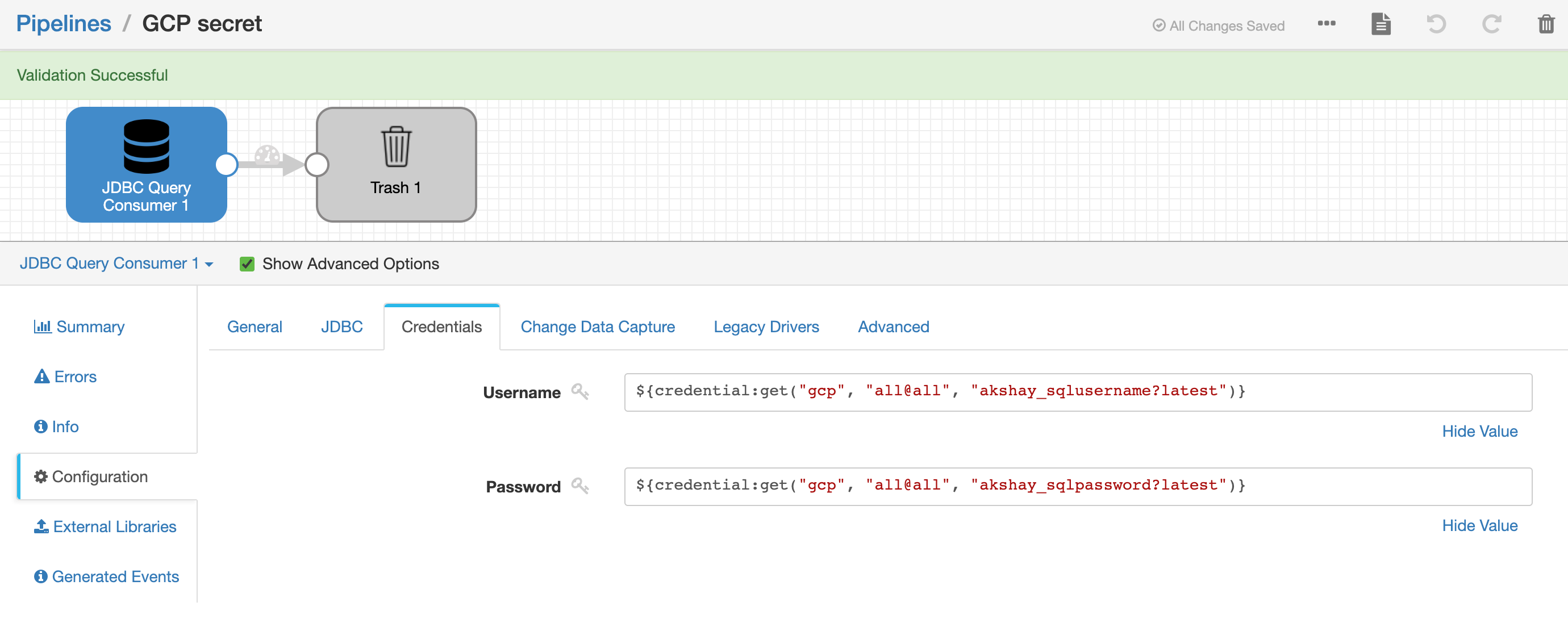
Once done, restart the data collector. This implicit EL expression we are going to use in the pipeline credentials pipeline:
Username => ${credential:get("gcp", "all@all", "akshay_sqlusername?latest")}
Password => ${credential:get("gcp", "all@all", "akshay_sqlpassword?latest")}
Where,
- gcp → credentialStores value.
- all@all → username@group
- akshay_sqlusername?latest → secret name ? version of secret i.e latest.